The Axios compromise is a useful reminder that most teams still talk about software supply chain risk at the wrong layer.
They focus on whether a package is popular, well maintained, or widely trusted.
That matters, but it was not the real failure here.
The real failure was letting trust propagate automatically through version ranges, dependency resolution, lifecycle scripts, and unattended update paths that most engineering teams barely inspect until something breaks.
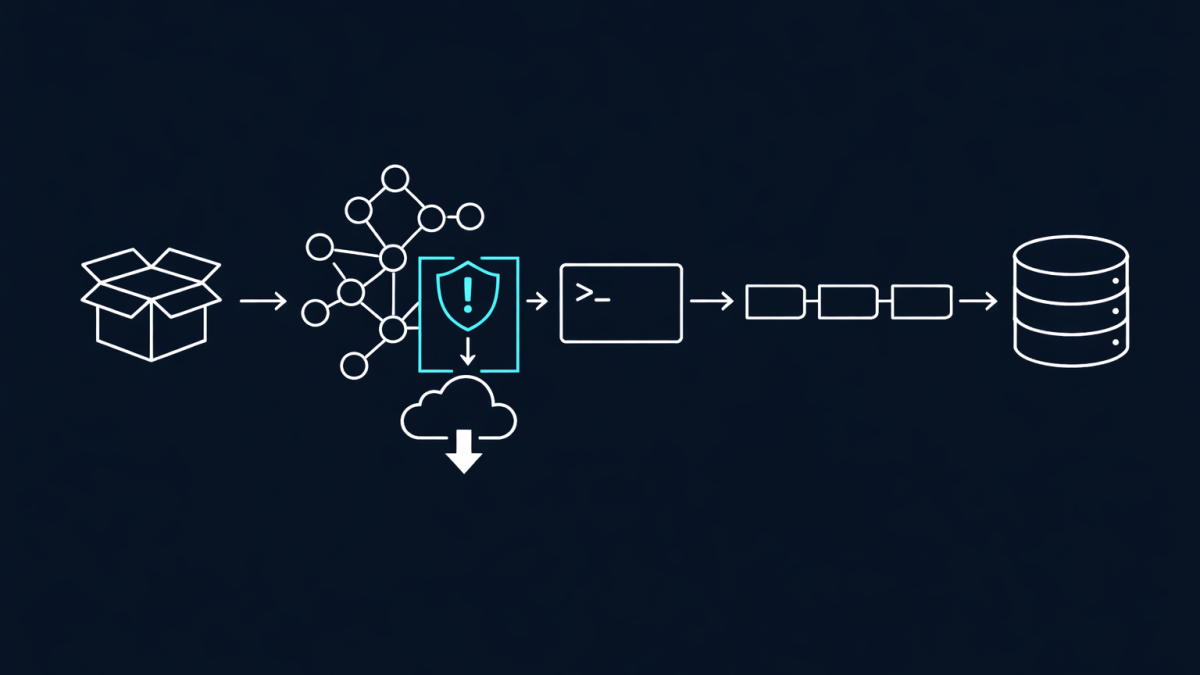
According to Microsoft Threat Intelligence, the malicious Axios releases were 1.14.1 and 0.30.4. The published Axios source code itself was not heavily rewritten. Instead, the attacker inserted a fake dependency, plain-crypto-js@4.2.1, which executed during install through a postinstall chain and pulled a second-stage payload from attacker-controlled infrastructure.
That detail matters more than most headlines suggest.
This was not just a story about one bad package. It was a story about how easily an organisation can inherit attacker code simply because its tooling assumes the newest allowed version is the safest version to trust.
The Package Was Trusted Before the Update Was Deserved
Axios has massive adoption. That is exactly why this attack worked as well as it did.
In most environments, a dependency like Axios is not evaluated every time it moves. It is approved once in principle, then allowed to keep changing underneath the business through caret ranges, tilde ranges, transitive resolution, dependency bots, CI rebuilds, and fresh developer installs.
That approval model is too loose for the way modern supply chain attacks actually land.
The compromise was effective because the install path itself was trusted. Teams assumed npm install was just package retrieval. In reality, npm install is also code execution when lifecycle scripts are available, and that means every update path is also a potential execution path.
The Most Important Technical Clue Was the Install-Time Behaviour
What stood out to me in Microsoft's analysis was how surgical the change was.
The attacker did not need to visibly sabotage Axios runtime behaviour. They only needed to add a dependency that looked plausible enough to pass casual scrutiny and then trigger execution during installation. That is a far cleaner way to compromise developer workstations and CI runners than shipping obviously broken application code.
Microsoft says plain-crypto-js@4.2.1 launched node setup.js automatically, contacted the Sapphire Sleet C2 domain, and delivered different second-stage payloads for macOS, Windows, and Linux. So the blast radius was not limited to one operating system or one narrow build scenario.
If your environment resolved to the malicious versions, your exposure began before your application even started.
That is why I do not see this as a dependency hygiene story alone. I see it as an execution trust story.
Auto-Updates Quietly Convert Governance Gaps Into Breaches
Most teams do not describe their dependency model as auto-updating, but many are doing it in practice.
If you use version ranges like ^1.14.0, allow transitive dependencies to float, accept dependency bot pull requests with shallow review, or rebuild containers against the open internet without strong controls, you have already delegated a meaningful part of your change management process to package ecosystems and automation.
That is convenient right up until an attacker learns how your convenience works.
The Axios incident exposed the operational weakness in that model. A package can be legitimate on Monday, compromised on Tuesday, and pulled automatically into developer endpoints, build agents, or deployment pipelines before anyone treats the change as a security event.
By then, the discussion is no longer about software composition analysis. It is about secrets rotation, endpoint containment, and whether your CI environment just became an intrusion path.
What I Would Change Immediately
If I were responsible for an engineering platform that touched Axios, I would treat this less like a package advisory and more like an incident response exercise.
- Pin Axios to a known safe version instead of using range-based upgrades.
- Use overrides to force safe versions through transitive dependency chains.
- Review CI and developer logs for axios@1.14.1, axios@0.30.4, or plain-crypto-js@4.2.1.
- Assume any secrets exposed to affected endpoints may need rotation.
- Disable or sharply limit postinstall execution where the workflow allows it.
- Reduce automated dependency updates for critical libraries until there is a human approval gate with real scrutiny.
Microsoft's guidance goes in the same direction: downgrade to safe versions, flush npm cache, inspect for the malicious dependency, rotate credentials, and restrict the update paths that allowed the poisoned release to land.
I would add one more principle.
Treat dependency updates as privileged change events, not background maintenance. The package manager is part of your execution surface now. Govern it that way.
The Bigger Lesson Is About Trust Boundaries
What I keep seeing across AI, software supply chain, and identity incidents is the same architectural failure pattern.
Teams extend trust further than they think they do.
They trust the vendor brand, then the package namespace, then the allowed version range, then the install process, then the automation wrapped around that install process. Eventually nobody can point to the exact boundary where explicit trust ended and inherited trust took over.
That is the real lesson in the Axios compromise.
The dangerous part was not just that a malicious package existed. The dangerous part was that so many environments were designed to consume it automatically once it appeared to fit the expected version pattern.
If your security model still treats auto-updates as harmless convenience, you are not really managing dependency risk. You are just waiting for the next trusted package to turn into an execution path.